Subscriber Benefit
As a subscriber you can listen to articles at work, in the car, or while you work out. Subscribe NowOf all the industries in the country, health care might be the juiciest for cyberhackers. And around central Indiana, institutions large and small are paying the price.
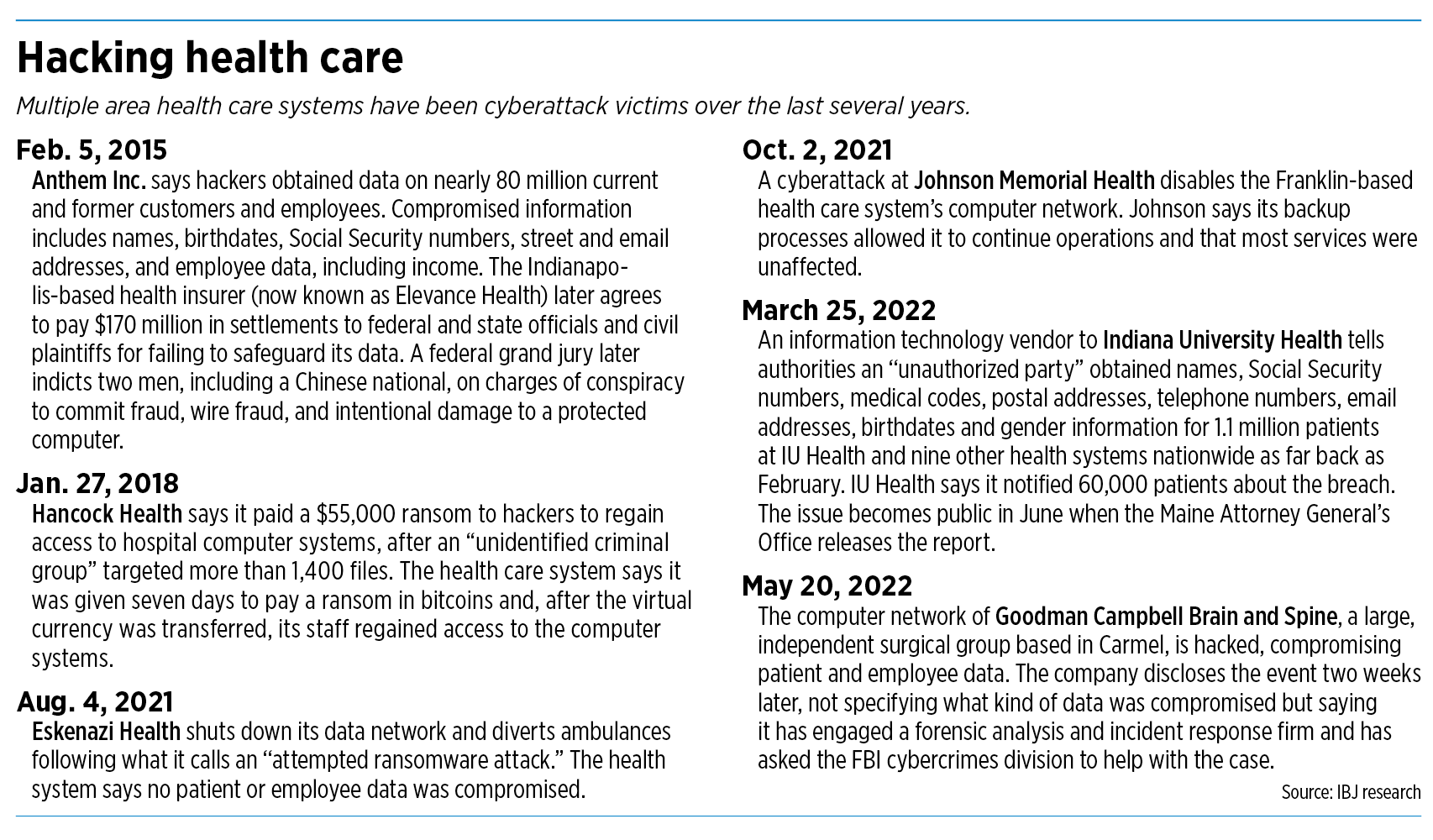
In the past few years, some of the region’s largest health care players—including Indiana University Health, Eskenazi Health and Elevance Health (formerly Anthem Inc.)—have seen patient or customer information compromised by hackers.
So have some of the area’s smaller hospitals, including Hancock Health and Johnson Memorial.
Hospitals, health insurers and medical clinics are loaded with patient and employee data that can be mined for identity and medical theft. Hackers can shut down computer systems for days or weeks, holding hospitals hostage until ransom is paid.
One of the latest attacks became public last month when the Maine Attorney General’s Office disclosed that a software vendor to Indiana University Health and nine other U.S. health systems was attacked.
The vendor, MCG Health, told authorities an “unauthorized party” obtained names, Social Security numbers, medical codes, postal addresses, telephone numbers, email addresses, birthdates and gender information for 1.1 million patients of about 10 hospital clients.
IU Health, the largest hospital system in Indiana, said it notified 60,000 patients about the breach, but declined to reveal details or answer further questions.
“Because this is MCG’s data breach, we recommend you contact them for information. They would have specific details relating to the breach,” IU Health said in a brief statement.
MCG, based in Seattle, did not respond to emails and phone calls from IBJ. Multiple class action lawsuits have been filed against the software company, a subsidiary of Hearst Health, in a federal district court in Washington state. The lawsuits allege negligence, invasion of privacy, breach of confidence and violations of consumer protection laws. IU Health and the other hospital systems were not named as defendants.
Nationally, cybersecurity breaches in the health care sector hit an all-time high in 2021, with nearly half of all hospitals in the country reporting an attack, according to a report from cybersecurity company Critical Insights.
All those attacks exposed protected health information for a record number of patients. In 2021, 45 million people were affected by health care attacks, up from 34 million in 2020, according to Fierce Healthcare, a trade news site.
And it’s not just hospitals that are feeling the heat. Attacks against health plans jumped nearly 35% from 2020 to 2021. And attacks against business associates, or third-party vendors, increased nearly 18% from 2020 to 2021.
Slow to upgrade
Some cybersecurity experts say health care is a soft target because many hospitals and other players have been slow to invest in new software that can stop or slow hackers. Instead, some hospitals are using their budgets to buy expensive new radiology hardware or surgical tools, and sticking with software that is decades old.

“Some are still running Windows XP on some of their systems,” said Tim Sewell, co-founder and chief technology officer of RevealRisk, a Carmel-based firm specializing in cybersecurity.
Fewer than half of health care organizations met national cybersecurity standards in 2019, even as cyberattacks grew in complexity, according to consultancy CynergisTek, based in Austin, Texas, as reported by Healthcare Dive, a trade news site.
Unlike some other sectors, health care is a relative latecomer to the digital revolution. For more than a century of the modern medical age, doctors and nurses have used paper charts to record patient information. The billing and coding office of hospitals were filled with binders and reference books. Even today, some hospitals continue to correspond by fax and mail.
Much of that changed about 15 years ago, when Congress passed financial incentives for medical institutions that used electronic health records, as well as penalties for those that failed to use them.

Within just a few years, what had largely been a pen and paper industry converted to electronic records, quickly building up a huge storehouse of digital information on patient conditions, diagnoses, treatments and outcomes.
“What that meant was that a lot of organizations were very quickly adopting advanced IT infrastructure,” said George Bailey, assistant director of cyber services at Purdue University. “They just didn’t have the skill sets. … The workforce wasn’t equipped to deal with the threat that came with that.”
By gaining access to sensitive health data, hackers can profit by selling the information on the dark web—the part of the internet where users can remain anonymous and untraceable.
Buyers can then use the medical information to commit identity theft by submitting fraudulent claims to Medicare and other health insurers, or by getting prescription drugs fraudulently and reselling them.

“Electronic medical records are actually more valuable on the dark web than credit card numbers or Social Security numbers,” said Reid Putnam, vice president of property and casualty at Gregory & Appel, an Indianapolis-based risk management and employee benefits firm.
Held hostage
Another big driving force: Hackers can shut down computer systems at hospitals and clinics, and demand ransom to unlock them. That can quickly throw a hospital into turmoil, as doctors and nurses are unable to pull up electronic health records to check a patient’s medications or lab results. It can also shut down surgical suites—the profit centers at many hospitals—and paralyze the administrative and billing offices.
At hospitals, every minute the computers are down, someone’s health is being put at risk.
“A good target is someone who pays ransoms quicker than most,” Putman said. “That can be a driving factor for why health care regularly is one of the top industry segments to get hacked.”
In 2018, Hancock Health paid a $55,000 ransom to regain access to hospital computer systems, after an “unidentified criminal group” targeted more than 1,400 files. Hancock said hackers gave the hospital system seven days to pay a ransom in bitcoins and, after the virtual currency was transferred, staff regained access to the computer systems.
In 2021, Eskenazi Health shut down its data network and diverted ambulances following what it called an “attempted ransomware attack.” The health system said no patient or employee data was compromised and that hackers did not gain control of its computer files. Eskenazi said it did not pay ransom.
Just a few months later, hackers attacked Johnson Memorial Health and disabled the Franklin-based health care system’s computer network. Hospital officials said their backup processes allowed them to continue operations and that most services were unaffected, although it took weeks to inspect all the files.
Indiana hospitals said they have invested millions of dollars in cybersecurity to strengthen their systems against attacks.
The average initial ransomware demand of health care businesses was $4.58 million, according to a report last year from BakerHostetler Data Security Incident Response Report. The average payout was $910,335.
Last year, the University of California San Francisco Health paid more than $1 million to hackers after a ransomware attack on its medical school’s computer servers.
“The data that was encrypted is important to some of the academic work we pursue as a university serving the public good,” the university said in a statement. “We therefore made the difficult decision to pay some portion of the ransom, approximately $1.14 million, to the individuals behind the malware attack in exchange for a tool to unlock the encrypted data and the return of the data they obtained.”
And ransom demands will continue as long as hospitals and other health institutions continue to write checks, some experts say.
“Many medical devices are legacy devices; they are older, so it is sometimes difficult to upgrade them,” cybersecurity expert Jack O’Meara told industry news site CyberNews. O’Meara is a director in the Advanced Solutions Cybersecurity practice of Washington, D.C.-based business consultant Guidehouse. He added: “Ransomware will continue to be on the rise, as long as health care organizations and hospitals are willing to pay.” •
Please enable JavaScript to view this content.

The explosion in data breaches is a direct result of their profitability fed by the underground world of crypto currency. Digital or crypto currency was specifically developed for underworld finance. The drugs trade at first. Now, it has exploded into an international climate and criminal threat. In some American and Canadian communities, crypto mining consumes nearly as much power as residential housing .
Holding digital currency should be made unlawful. For individuals it is nothing more harmful than a “greater fool” bet and for climate change, an accelerant. But, for the criminal electronic underworld, it is the staff of life.
Domestically unlawful or internationally unlawful? And what do you propose to do with countries which either don’t care about crypto’s legality (e.g. Russia); who advocate it (e.g. Nigeria, Kenya; Switzerland, Denmark, France,…I could easily name another dozen OTTOMH), have embraced it as national currency (e.g. El Salvador); or are preparing to endorse it in the near future (e.g. China in 2023)? And you’re going to have to educate Congress Critters who don’t know a bit from a nybble from a byte.
.
Wouldn’t it be easier to find out why the number of stories about US businesses being hit could have avoided it with MFA or widespread password changes when someone leaves? How about finding ways to detect it in progress because it takes 3-4 days for an attack to become complete? What about educating employees who are sent compromising email and however well-intentioned they are, they more or less hand over the information (good social engineering) which is then used? And last, but not least, why we hear/read so many stories about companies which have been hit but the number of businesses which say, “yes, we got clobbered but we got our backups out of the safe, restored, and we only lost 3-4 days of data, not a complete disaster.” ??? Could it be businesses aren’t backing things up religiously like when mainframes were the primary hardware? WRT this last issue (backups/restores), I’m betting the percentage of companies (of any size) which actually do good backups can be counted (at best) on 10 fingers but would be willing to put some money on the number of fingers on one hand. It’s kind of like the old saying, “Never bet what you aren’t willing to lose”.
.