Subscriber Benefit
As a subscriber you can listen to articles at work, in the car, or while you work out. Subscribe NowCybersecurity expert J.J. Thompson has been proofing computer systems against malicious attacks for decades. But he didn’t realize how far the ransomware threat had permeated Indiana until a couple of years ago, when he ate lunch in a tiny diner near Tipton.
“I was listening to farmers talk about ransomware,” he recalled. “You know something is a global problem when farmers in Tipton are sitting in a diner, eating tenderloins and talking about their fear of getting ransomware on their tractors.”

Ransomware is a specialized form of malware that often infects computers (including those on tractors) via email attachments. Click on the attachment, and software instantly encrypts the system’s data, making it impossible to access until the victim pays a ransom that can range from a few hundred dollars to north of a million.
If the victims pay, they typically receive a set of encryption keys allowing them to unlock their information.
“We’ll see continuing ransomware-like attacks, and they’re going to be made nastier and nastier,” said Thompson, founder of Indianapolis-based Rook Security and now senior director of managed threat response for Sophos, a United Kingdom-based security company that purchased Rook in June.
No one’s quite sure how often such incidents happen in Indiana, but all experts agree that the number of infiltrations and attempted infiltrations is rising.

In the winter of 2016, a Madison County attack locked up most of the county’s systems, forcing the police to revert to writing paper tickets until the city paid a ransom of $21,000. And this year, LaPorte County forked over $130,000 (about 10.5 bitcoin, the preferred medium for ransom payments) when its systems were infected.
According to Doug Rapp, president of the Cyber Leadership Alliance (a Hoosier not-for-profit that brings together state experts to, among a great many other things, promote cybersecurity), Indiana attacks are becoming not only more frequent, but more precisely targeted.
“We’re seeing a rise in two particular areas—government and health care,” Rapp said.
He said criminals know if they are able to lock up information protected under the Health Insurance Portability and Accountability Act of 1996—known best as HIPAA—health providers are more likely to pay the ransom. That’s because they can face fines if the information is spilled onto the internet.
“And schools have a lot of personal information, particularly about minors, so that’s a lucrative target,” Rapp said.
Attackers who use ransomware range from lone wolves to well-organized international crime syndicates to rogue nations, he said.
“We used to joke about a certain country,” Rapp said. “When their government cybersecurity employees got off work, you could see an immediate rise in criminal enterprises. I won’t mention Russia’s name on that.”
While major corporations and large government agencies have taken detailed, elaborate steps to guard against the problem, smaller municipalities, companies and organizations are in something of a bind. Protecting such small groups against ransomware (or at least improving their chances of recovering from an attack) can be time-consuming and costly.
That might explain why so many attacks are now targeted at just such second- and third-tier targets. They can’t pay as much, but they’re also far, far more likely to have exploitable vulnerabilities such as primitive, ad hoc computer systems, tiny IT staffs, and a tendency not to install software patches promptly.
“There are criminal enterprises out there that are just trolling for vulnerabilities, and they don’t care if you’re a bank or a liquor store,” Rapp said. “They’re just looking for an unsecured internet connection. There’s no set of businesses that’s untouched.”
Many malware-infected institutions choose to pay ransoms, given that catching the people responsible, or even identifying them, is often next to impossible. Small businesses sometimes don’t even know to whom to report such incidents. And no one’s quite sure how many attacks happen in Indiana, because many victims are reluctant to acknowledge them.
“Nobody wants to highlight where these things have happened,” Rapp said. “People in general, across the board, don’t like to talk about breaches. It’s always been a problem when you try to collect information. People don’t like to share their vulnerabilities.”
But not everybody who’s experienced a ransomware attack keeps quiet. That certainly wasn’t the case for Hancock Regional Hospital, a 100-bed Greenfield facility that had all its files locked up by hackers in January 2018. Instead of lying low, Steve Long, president and CEO of Hancock Health, started blogging about it almost immediately.
“We made the decision early on to be very transparent because we felt our community deserved to know what happened,” Long said.
Since then, the hospital system has shared details of the incident during an appearance on “60 Minutes” and at some 30 meetings around the country.
“Everybody is concerned about reputational risk,” Long said. “That’s why they don’t say anything. But I can tell you that, in our local community, we have had overwhelmingly positive feedback about our transparency.”

The lesson Long shares with other CEOs is that, while preparation for an attack can blunt its consequences, it often can’t prevent it. After all, his hospital system wasn’t exactly wide open. It had run phishing tests on emails to make sure workers didn’t open dicey-looking files, hired a company to test the network for penetration threats, and used another firm to watch at all times for intrusions.
“We were pretty average to above-average prepared,” Long said. “We had everything in place that you would expect.”
All to no avail. The hackers uploaded the ransomware using credentials issued to a vendor, which were purchased on the dark web. The hospital’s antivirus system caught that first attack, but the invaders persisted.
“They changed the signature of the virus and it went right past our protection,” Long said. “Unfortunately, the company we were paying to monitor our network all the time didn’t catch it.”
The hospital’s computer system was completely frozen, and its staff thrown back into the Stone Age. Or at least, the 1950s.
“We had zero computers running, aside from patient-facing equipment like IV pumps and things like that,” Long said. “Everything else was shut off.”
Since there was no way to rapidly restore their systems without the encryption keys they were offered if they agreed to the ransom, the hospital opted to pay about $55,000 in Bitcoin to obtain them.
There’s little hope the perpetrators will ever face justice, even though the FBI was able to identify them.
“They were a couple of guys from Iran,” Long said. “The FBI has extradition warrants against them, so if they ever leave Iran and go to a country with an extradition agreement with the U.S., they will be captured and brought here.”
The hospital system now has even more stringent precautions in place. Long said he can watch his facility get (so far unsuccessfully) attacked multiple times each day by yet more ransomware.

Fred Cate, senior fellow at Indiana University’s Center for Applied Cybersecurity Research, said such threats are as pervasive in cyberspace as airborne bacteria is in the real world.
“If you buy a new computer, take it out of the box and plug it in, from the moment you access the internet, it will get its first malware attack in about seven seconds,” Cate said.
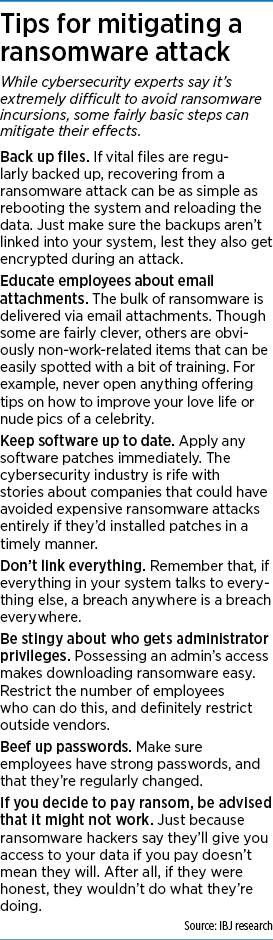
However, he (along with other experts) said smaller organizations can take some fairly straightforward steps to ward off an attack or, at the very least, mitigate its effects. For instance, apply software patches immediately, train employees not to open suspicious email attachments and remember that not everything in your system has to be connected. If, for instance, payroll is kept on an isolated system, it won’t go down if the main system is successfully attacked.
“We’ve gotten this notion that my refrigerator has to be able to turn on my lights and talk to my car,” Cate said. “That means a vulnerability in one of those is now shared with all of them.”
The best precaution is to regularly back up critical files and store them offline. That way, if your data is encrypted by ransomware, in theory all you have to do is reboot and download the stored information.
Ideally, everything should be backed up nightly, with the file physically stored in a vault. But that could be an onerous and expensive chore for small companies and government entities.
“For most school districts and utilities, that’s not the level at which they’re operating,” Cate said. “They might have one IT employee, not an army of people.”
The answer, he said, is to still do backups, but less frequently. That’s far, far better than nothing.
“If you can’t afford Grade A backups, have Grade B backups,” Cate said. “At my house, I back up twice a month. So if you compromise my data, the most I risk losing is two weeks. Don’t let the perfect be the enemy of the good.”•
Please enable JavaScript to view this content.


(from above)
*Be stingy about who gets administrator privileges.*
.
Possessing an admin’s access makes downloading ransomware easy. Restrict the number of employees who can do this, and definitely restrict outside vendors.
.
======================================================
.
This is fine for power users and large businesses but something home users and single-machine/small businesses need to understand is this:
.
*** Microsoft is not in the security business. They are in the “it just works” business.***
.
Let’s say you just opened a small floral shop called “Best Blooms” and you’ll have a single PC (which includes laptops) which will manage your books, do your various online work, etc. You take your bright, shiny, new PC out of the box, you look at the instructions, and you’re told that when prompted, create a userID and specify a password. You create a userID of “BestBlooms” and specify a password, and you’re now the proud parent of a bouncing baby PC running the latest version of Windows and you feel like a real business owner, now probably more qualified to grill, er, interview Mark Zuckerberg before Congress than all of the Congress Critters combined because they’ve never done what you just did, let alone played Solitaire.
.
You’ve heeded the warnings about not giving anyone administrator privileges because your new machine never asked you a question when you created “BestBlooms” along the lines of, “Is this an administrator userid?” because you’d probably say, “No”, right?
.
Wrong. The userID “BestBlooms” is now an administrator userID because Microsoft makes sure the first userID you create is an administrator. That way, if anything has to be done and you’re following instructions from Microsoft, a magazine, a book, online, etc., you won’t get a message along the lines of, “Insufficient Authority”. Remember, Microsoft is in the “It Just Works” business and they don’t want to stand in the way of you getting your machine set up & running…easily. They don’t tell you you’ve just exposed your machine to all sorts of unforeseen dangers because *they aren’t in the security business*. In their eyes, their responsibility to provide security ends after you’ve created a super-secret password that only you (and anyone you share it with) know.
.
So when you get yourself connected to the Internet and start sending and receiving email, and someone named Susan (we all know a Susan, or Bob, or Mike, or Christy) sends a message which says, “This is what I was telling you about…” with an attachment, you click on it. After all, it doesn’t look like all of the other messages you read about which looks like a three year-old wrote in broken English and makes no sense..
.
*Boom!* You’ve just exposed your machine to whatever that attachment is…even if you’re running some type of software everyone you know told you go get which is supposed to protect your machine. (That attachment is commonly known as a “payload”…as in a bomb.) And why does it happen? Because you’re an administrator.
.
So how do you avoid it? Instead of making your first userID something like “BestBlooms” you specify something like “God”. Now, if that offends your religious sensibilities, come up with some other name like “Admin”, short for “Administrator”. (Personally, I prefer “God” because that’s what it can do on your machine — just about anything which can be done, “God” can do it. After you’ve set up your machine and have everything ready to go, THEN you create the userID “BestBlooms” and you make sure it’s not an administrator. And you sign onto “God” only to do things you need “God” to do, then you sign off and sign back on to “BestBlooms” so you’re just a regular user.
.
Does this mean you’re safe? No, but you’re safeR [sic] than your first userID being “BestBlooms” and remaining paranoid every time you do something which stands to have a rotten payload that could do as much damage to your PC as if you were to pour a can of gas over it and light a match. Heaven forbid you be careful, never have a problem, then have someone in your office sit down and click on an email attachment (reread about pouring gas).
.
What else can you do? That’s another story for another time. I’m just trying to save you from electronically pouring a can of gas over your machine and just wait for someone to email you a lit match.
.